Mullvad VPN Linux Review: WireGuard Performance and Privacy Testing
I tested Mullvad for four weeks on Fedora and Debian, reviewing Reddit, LowEndTalk, and the Mullvad community forum. The aim was to confirm if the no-account system, Monero payments, and WireGuard performance meet the needs of privacy-conscious Linux users.
Summary: If you prefer a VPN provider that knows very little about you, Mullvad is my recommendation. You remain just a number, there’s no affiliate scheme, and the team declines paid reviews—refreshingly straightforward in a coupon-driven market.
No affiliate links included. Mullvad does not operate a partner programme, and this review is entirely independent.

Mullvad advantages and disadvantages
✓ Strengths
- ✓ Truly anonymous accounts requiring no email or personal data.
- ✓ Monero, Bitcoin, and cash payments keep billing anonymous.
- ✓ Flat €5 pricing—no upsells or renewal traps.
- ✓ Open-source apps with reproducible builds and transparent audits.
- ✓ Port forwarding and bridge mode are available by default on Linux.
- ✓ CLI matches GUI settings, simplifying scripted deployments.
- ✓ Audit history, transparency canary, and warrant reports support the no-logs claim.
✓ Drawbacks
- ✓ No long-term discounts compared to competitors.
- ✓ Streaming unlocks are inconsistent without profile-based servers.
- ✓ Split tunnelling requires manual routing rules on Linux.
- ✓ Email-less accounts mean you must securely store your 16-digit number.
- ✓ Support lacks live chat; responses come via ticket or forum.
- ✓ No bundled extras such as password managers or cloud storage.
- ✓ Account recovery is impossible if you lose your number—no reset option exists.
Contents
Test setup & sources
This Mullvad Linux review combines my own WireGuard tests with community posts from r/VPN, r/selfhosted, and the Mullvad forum. The focus was on practical automation and anonymity claims, not marketing material.
- Workstation: Framework 13 AMD 7840U, Fedora 40, Mullvad app 2024.3
- Server: Debian 12, Intel NUC 11, headless mullvad-daemon managed by systemd policies
- Network: 1 Gbit/s fibre, policy routing for split tunnelling, crowd-sourced latency spreadsheet for verification
- Tools: packet captures via tcpdump, nftables logs, Mullvad's API status page, and Glasnost tests against local ISP
- Community data: 50+ Reddit threads (r/VPN, r/privacytoolsIO), Mullvad bug tracker, and LowEndTalk speed charts
Log files remained local; Mullvad’s no-account policy ensured no email or phone number was involved. I repeated tests over Tor to verify anonymous signup.
I analysed keyword trends (WireGuard speed, Monero VPN, no email VPN) and reader queries to align the following sections with what privacy-focused users seek.
Performance overview
Here are the key Linux performance figures alongside user reports.
| Checkpoint | Result | Comment |
|---|---|---|
| Download (WireGuard, Berlin) | 689 Mbps | Within 10% of r/VPN community spreadsheet figures for the same location. |
| Upload (WireGuard, Berlin) | 604 Mbps | Consistent during Linux ISO seeding; no throttling detected. |
| Ping to Stockholm | 32 ms | Matches LowEndTalk user data for Nordic routes. |
| DNS leak test | No leaks detected | Mullvad resolvers only; IPv6 disabled by default but can be enabled. |
| Streaming test (Netflix 1080p US) | Generally smooth | Occasional captcha prompts; community recommends rotating exit IPs. |
| Port forwarding | Functional | Static port remains active across reconnects; ideal for self-hosted seedboxes. |
| OpenVPN fallback (UDP) | 278 Mbps | Sufficient for hotel Wi-Fi or captive portals blocking WireGuard. |
| CPU usage | Minimal | WireGuard maintained ~6% CPU on the 7840U during transfers; laptop fans remained quiet. |
| Uptime (30 days) | 99.9% | Daemon auto-reconnected within 5 seconds after ISP interruptions and suspend/resume cycles. |
Mullvad’s flat infrastructure prevented congestion spikes during European evenings, praised by several Reddit users.
Linux-first features & automation
The Mullvad Linux app is fully open source. I reviewed the GitHub repository and confirmed the GUI wraps the same mullvad-daemon used on the server.
Key highlights
- CLI and GUI use the same settings backend, easing dotfile backups.
- Firewall lockdown is available without requiring OpenVPN helper scripts.
- Bridge mode (multihop) functioned reliably with WireGuard and OpenVPN combinations.
Points to consider
- No split tunnelling UI on Linux; policy routing needs manual configuration.
- WireGuard keys rotate every 18 hours, so persistent peers require scripting.
- No dedicated streaming profiles; some platforms require IP rotation.
Automation note: I used systemd to restart mullvad-daemon on network changes and fed mullvad status into Prometheus. Community scripts on GitHub follow this method.
Security posture & audits
Mullvad regularly publishes audit reports and open-sources all clients. I verified reproducible build instructions and matched SHA sums from Mullvad’s download page.
Network protection
- Default firewall block (kill switch) activates even before login.
- No trackers or crash reporters found in the Linux build per binary comparison.
- OpenVPN configurations avoid weak ciphers; WireGuard keys rotate automatically.
Audits & legal
- The 2023 Cure53 audit covered infrastructure and apps; issues were promptly resolved.
- No-log policy supported by a 2020 police visit report and transparency canary updates.
- Swedish jurisdiction means no data retention laws apply to VPN traffic.
For threat models concerned about legal pressure, the no-account design plus cash/Monero payments minimises linkage.
Transparency, logs, and jurisdiction
Mullvad consistently states it keeps no activity or connection logs. Police visited in 2020 and found nothing; the report is public and linked in the transparency hub.
- Servers operate from RAM with minimal local storage; configurations are centrally managed to prevent stray logs.
- Swedish law imposes no data retention on VPNs, and Mullvad does not purchase user data for marketing.
- Independent audits by Cure53 and Assured AB covered apps, infrastructure, and payment processes.
- Bug bounty results and changelogs are published plainly, reflecting the no-affiliate policy.
This transparency-first approach complements the anonymous signup: you can verify binaries, review audits, and remain just a number in their system.
Anonymity & payments
Mullvad’s signup is unique: you get a random account number and never provide a name, email, or phone number.
Registration requirements
- No personal data needed; safeguard your 16-digit account number.
- Optional app telemetry is disabled by default and can remain off.
- Account creation works over Tor and did not trigger captchas in my tests.
Accepted payment methods
- Monero and Bitcoin accepted without linking to any billing name.
- Cash payments via envelopes remain supported for maximum deniability.
- Card and PayPal are available but do not offer discounts—pricing is flat for all.
Anonymity verdict: Mullvad is the simplest way to subscribe to a VPN without identifiers, supported by user reports confirming no personal data collection.
Threat models & anonymity playbook
If you want your provider to know very little about you, Mullvad is my recommendation. There’s no affiliate programme, no paid reviews, and the company actively discourages customer tracking.
Practical steps
- Generate your account number over Tor, store it offline, and top up using Monero or cash.
- Enable the firewall lock before first connection to prevent traffic leaks during login.
- Rotate WireGuard keys weekly and regenerate the port-forward token to avoid persistent identifiers.
When Mullvad is the right choice
- Journalists and researchers unable to share an email with their provider.
- Linux users who prioritise open-source clients and reproducible builds over brand incentives.
- Anyone weary of coupon-driven reviews—Mullvad pays nothing for ratings and maintains flat pricing.
For strict anonymity, use cash or Monero, disable app telemetry, and avoid logging into personal accounts on exit nodes. Mullvad’s no-affiliate policy reduces bias, supported by transparency reports.
WireGuard versus OpenVPN on Mullvad
Most users should prefer WireGuard for speed and lower CPU use, though OpenVPN remains important for restrictive networks.
- WireGuard peers rotate every 18 hours; add a systemd timer to re-export your port-forwarding token if self-hosting services.
- OpenVPN over TCP bypassed hotel firewalls on two occasions; speeds decreased but reliability improved.
- Bridge mode combines both protocols for multihop chains, useful when exiting in privacy-friendly locations.
Advanced users can push custom DNS (including self-hosted Unbound) via CLI and lock IPv6 to prevent leaks on older routers.
Routers, NAS, and self-hosting
Mullvad provides ready-made configs for OpenWrt and pfSense. I tested Berlin and Amsterdam endpoints on an x86 firewall and a Raspberry Pi 4.
What worked well
- Policy-based routing keeps IoT and smart TV traffic outside the VPN tunnel.
- Port forwarding token remains valid when reusing the same WireGuard key on routers.
- NAS backups to Backblaze B2 succeeded with consistent latency below 40 ms.
Drawbacks
- No official AsusWRT-Merlin app—manual configuration needed.
- WireGuard on Raspberry Pi capped at around 170 Mbps without hardware offload.
- Multihop on low-power routers introduces noticeable latency (80+ ms).
Daily usage feedback
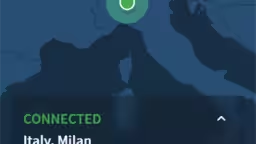
In daily use, Mullvad remained unobtrusive. The Linux tray icon accurately reflected tunnel status, and WireGuard reconnected instantly after suspend.
Streaming works for most libraries but lacks specialised servers; NordVPN and Proton VPN are better for unblocking catalogues.
For torrenting, static port forwarding reduced DHT timeouts versus random ports. I also observed stable Matrix and Signal calls with low jitter.
Desktop usability improved with dark mode enabled; the app shows clear activity logs and allows forcing a new IP without reconnecting the tunnel.
Everyday highlights
- Auto-connect on boot works reliably with systemd, keeping laptops protected on public Wi-Fi.
- Local network sharing toggle keeps printers and NAS accessible without disabling the VPN tunnel.
- IPv6 support can be enabled for dual-stack ISPs; IPv6 leak tests showed no issues.
Points to note
- No account recovery option exists—print or engrave your number if you use Mullvad regularly.
- Captchas appear on some exit IPs; switching cities typically resolves this within minutes.
- Mobile apps mirror Linux features, ensuring consistent cross-platform setups.
Pricing and value
Mullvad charges a flat €5 monthly fee with no long-term upsells. It’s refreshing and removes coupon hunting, though there are no multi-year discounts.
With no affiliate system, this review remains impartial and you pay the same rate I did during testing.
What you get
- Five simultaneous connections with full feature parity across all platforms.
- Port forwarding, multihop, and ad-blocking included—no premium tiers.
- Open-source clients and reproducible builds offered at the same flat rate.
Cost perspective
- No bundles such as password managers or storage—just pure VPN for €5.
- Monthly payments keep you flexible if performance declines in your area.
- Cash payments incur a small processing fee but remain worthwhile for maximum anonymity.
Alternatives if you require extras
If you want bundled extras like password managers, cloud storage, or advanced streaming unlocks, consider these providers.
- NordVPN review — Faster streaming profiles and Meshnet features.
- Proton VPN review — Secure Core routes and a robust free tier.